From weather snippets, website logins, and travel bookings to embedded finance, streaming services, and vehicle software updates, APIs (Application Programming Interfaces) are everywhere. They play a critical role in the economy by allowing different applications to share data and functionality.
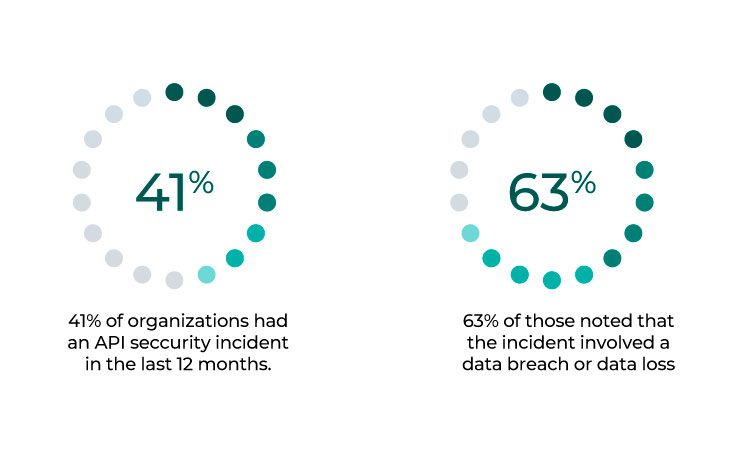
However, as APIs become increasingly commonplace, they are also becoming a more attractive target for cybercriminals. A recent study by Noname Security found that 41% of surveyed global companies with over 3,000 employees experienced an API-related security incident in the past year. The research pool consisted of IT experts from diverse industries, representing 350 organizations in total. Almost a third of all incidents involved a data breach or loss.
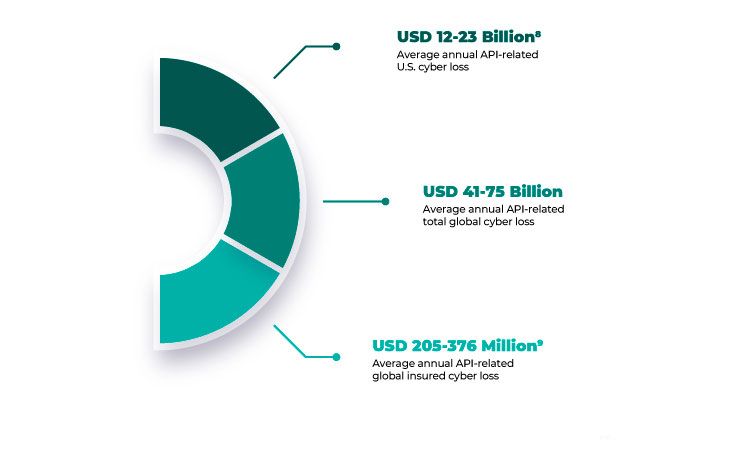
Another study by Imperva that analyzed almost 117,000 security incidents found that API insecurity costs organizations up to $75 billion annually.
Clearly, when it comes to APIs, cybercriminals are relentless, and the resulting loss of data or breach can end up costing your organization billions in financial losses and damage to its reputation.
So, how can you ensure that your API is secure? Here are ten best practices to follow:
Have a Robust API Security Strategy
API security starts with a comprehensive security strategy. Unfortunately, a recent study by Salt Security found that only 9% of organizations have an advanced API security strategy.
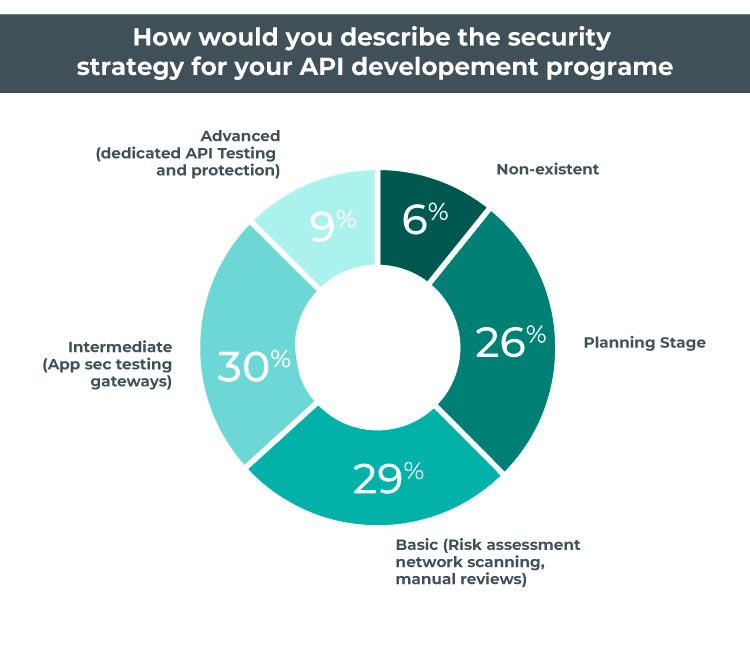
With API reliance at an all-time high and with many critical business processes and data moving through APIs, organizations must take the time to develop a strong API security strategy. This strategy should address the vulnerabilities and risks associated with APIs and outline the steps to mitigate these threats.
API Security Authentication and Authorization
You can mitigate a broad range of attacks by ensuring that only authorized users have access to your API. One way to do this is to implement strong authentication methods such as multi-factor authentication. Another option is to use an identity management system that integrates with your API. Also, ensure that data passed through your API is encrypted. This will make it more difficult for attackers to intercept sensitive information being exchanged between different systems. SSL/TLS encryption should be used for all data in transit.
Improve Logging Practices
In order to detect and investigate suspicious activity, it’s important to have robust logging in place. This includes logs of all API access attempts (both successful and unsuccessful). These logs should include information such as the user’s IP address, the time of the access attempt, the API method used, and the parameters passed. This data can be extremely valuable when investigating a security incident.
Avoid Misconfiguration
One of the most common causes of API security incidents is misconfiguration. This can include things like leaving debug mode enabled, using weak passwords or failing to properly restrict access to sensitive data. Therefore, it’s important to regularly review your API configuration to ensure that it is secure.
Avoid Unnecessary Data Exposure
Another common cause of API security incidents is exposing too much data. This can happen if you allow direct access to sensitive data or fail to sanitize input parameters properly. When designing your API, only expose the data that is absolutely necessary.
Integrate API Security Testing (AST) Into Developer Pipeline Activities
In the Noname Security study we referenced earlier, 87% of respondents stated that more effective API security testing (AST) integration into developer pipeline activities could prevent project delays occasioned by API security concerns. Therefore, API security testing should be a key part of your development process. In addition, automated testing tools can be used to test for various security issues, such as SQL injection and cross-site scripting (XSS).
Automate API Inventory Update Processes
As your organization’s API portfolio grows, keeping track of all the APIs in use becomes more difficult. In the Salt Security Study, 42% of respondents said that their biggest worry is outdated or “zombie” APIs. To address this issue, it’s crucial to automate the process of updating your API inventory to get rid of or deprecate previous versions.
Monitor APIs for Attacks
It’s important to continuously monitor your APIs for attacks. This can be done using a web application firewall (WAF) or by implementing API-specific security controls. You can quickly detect and respond to suspicious activity by monitoring attacks.
Rate Limit API Responses
Rate limiting is a technique that can be used to throttle API responses. This can help prevent denial-of-service (DoS) attacks and protect against other types of abuse. When rate limiting, it’s important to consider things like the type of API being used, the frequency of requests, and the desired response time.
Breakdown the Silos Between Security and Development Teams
Finally, breaking down the silos between security and development teams is important. To effectively secure your API, it’s essential to have close collaboration between these two groups. These groups have historically been at odds, but by working together, they can ensure that security concerns are addressed early in the development process. Given these challenges, security teams must find ways to allow app developers to write secure code quickly and efficiently. One way to do this is by deploying solutions that include API discovery and data classification. This approach will help analysts understand how APIs work, identify potential vulnerabilities in the data flowing through them, and test for weaknesses.
If you need to build or improve your API functionality to increase your business outcomes, Expeed can help. We have the experience and expertise to develop an API that meets your specific needs and helps you achieve your business goals. Contact us today to learn more about our API development services.

Expeed Software is a global software company specializing in application development, data analytics, digital transformation services, and user experience solutions. As an organization, we have worked with some of the largest companies in the world, helping them build custom software products, automate processes, drive digital transformation, and become more data-driven enterprises. Our focus is on delivering products and solutions that enhance efficiency, reduce costs, and offer scalability.


